Commercial Cyber Security
It is estimated that by the end of 2021, the global economy would bear the loss of US$6 trillion due to cyber attacks. With more and more people working from home, cyber security has become more than important than ever.
Cyber Security Benefits
Critical Infrastructure Cybersecurity
In recent years cyber attacks on business have risen over 300%. More employees are working from home and the opportunity of attacks on businesses through remote workers has become more apparent. Educating and training employees on cyber security prevents intrusion of vital coporate information.
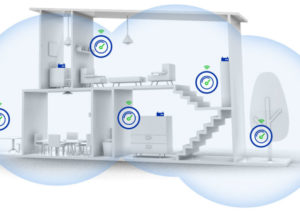
Network Security
Secure computer networks from intruders, targeted attackers, and opportunistic malware. Continuous cyber security upgrades help prevent these types of attacks. We provide expert advise and services to maintain your networks security.
Cloud Security
With the growth of cloud technology, this has created a new opportunity for intrusions of privacy and theft of personal data. Prevent unwanted users from extracted passwords, card number and other personal information connected to your home’s network.
Types of Cyber Security
- Anti-virus programs
- Firewalls
- Monitored Internet Access
- Encryption
- Firewalls
- Ransomware and phishing protection
- Brute Force Attack prevention
-
Tamper prevention
Top 6 Cyber Security Threats to Businesses in 2021
Exploitation of Remote Work
Even with the end of the COVID-19 in sight, organizations have no intention of returning to a full on-site worksite. From the beginning of the pandemic to now, employess working from home left security gaps that are actively exploited by cybercriminals.
Phishing
Phishing is one of the most common types of cyberattacks, mainly because it is often an effective technique for gaining access to an organization’s network and systems. It’s usually easier to trick an employee into handing over sensitive data
As a result, phishing will continue to be a problem into the future as long as it remains effective.
Cloud Security
The affect of working from home causes oraganzitations to share information via the cloud. Companies needed the accessibility, flexibility, and scalability offered by cloud-based solutions. Cloud security technology lags behind the rapid adoption of organizations adopting cloud technology.
The Rise of Double-Extortion Ransomware
The ransomware industry has also experienced numerous innovations in recent years. Ransomware as a Service (RaaS) operators develop and sell ransomware, expanding their reach and providing less sophisticated threat actors with access to high-quality malware.
Another recent trend is the “double extortion” ransomware campaign. Instead of simply encrypting files and demanding a ransom for their recovery, ransomware groups now steal sensitive and valuable data from their victims as well. If the target organization does not pay the ransom, this data is posted online or sold to the highest bidder.
An Epidemic of Healthcare Cyberattacks
During the COVID-19 crisis, the healthcare sector became more vital than ever. Hospitals and other healthcare providers around the world were overrun with patients as a result of the pandemic
.In many cases, the focus on patient care took away focus and resources from cybersecurity in these organizations. As a result, an industry that already struggled with cybersecurity was left even more vulnerable to cyberattacks.
A New Focus on Mobile Devices
The popularity of corporate mobile devices has been steadily growing in recent years. Employees can be more productive when permitted to use the devices that they are most comfortable with.
With the growth of remote work, this trend is unlikely to reverse itself. Employees working from home or from anywhere are more likely to use mobile devices than those working from the office. With the increased use of mobile devices for business purposes comes new cybersecurity risks. Cybercriminals are increasingly targeting these devices in their attacks, and many businesses lack the same level of security on their mobile devices as they have on traditional computers.


Networking between audio, video, data, and voice systems seamlessly

Everything you need to create, deploy, and play any type of content on any screen or media player.